With Indian organizations growing in terms of size and operation in various sectors like IT parks, manufacturing units, logistics centers, and corporate campuses, among others, securing physical premises is one of the major concerns facing these enterprises today.
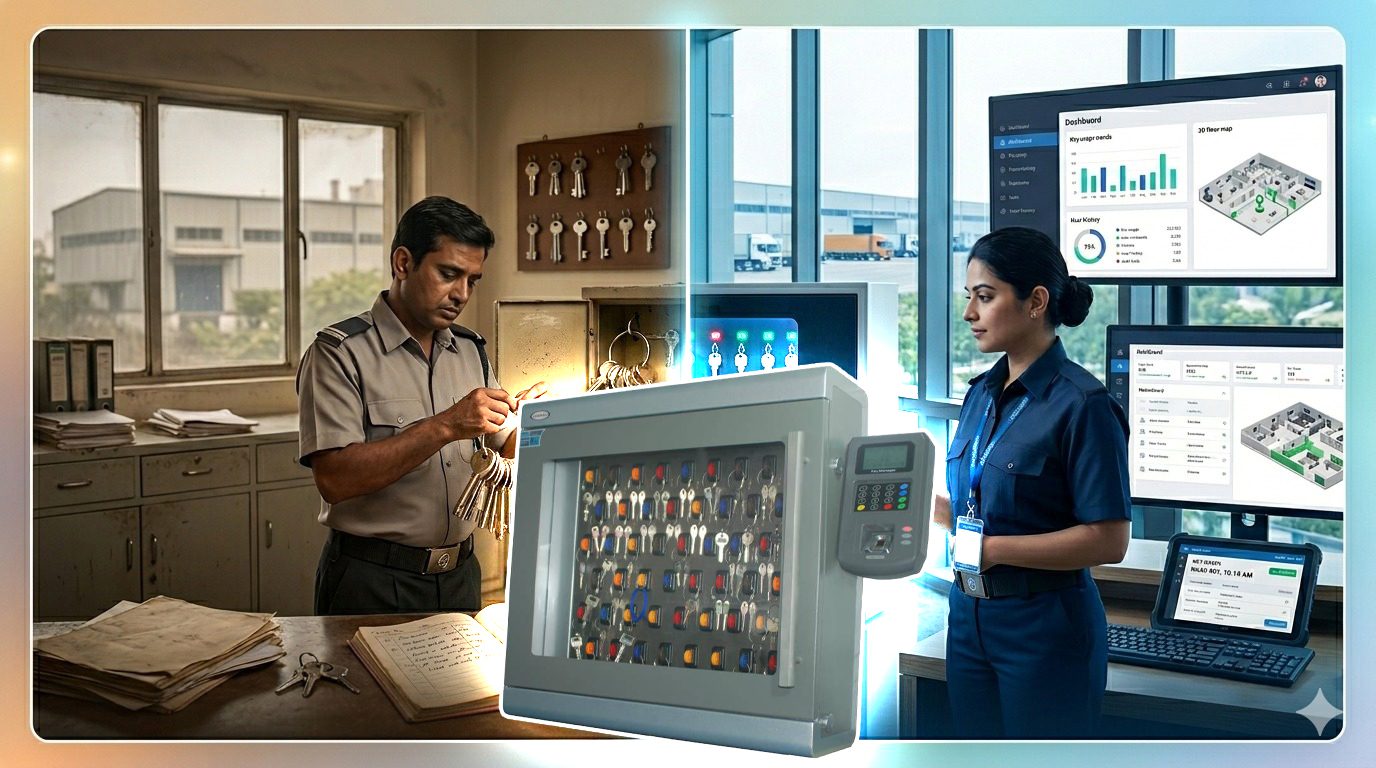
Key management systems refer to processes through which physical keys are stored, monitored, and managed in enterprises. These systems are essential in ensuring that there is complete traceability of the physical keys and that they are only accessed by individuals authorized to do so.
For Indian organizations, especially those running in different departments with restricted areas and valuables, key management systems are an indispensable part of physical security. In this blog, we will explore how key management systems are strengthening physical security across Indian enterprises.
Importance of Secure Management of Physical Keys in Business Organizations
Although the use of digital security solutions is rapidly increasing, physical keys are still commonly used by businesses. Rooms in offices, data centers, storage areas, locker rooms for equipment, and parking garages commonly employ conventional locking mechanisms. If physical keys are not well-managed, they pose risks to the organization.
The manual management of physical keys typically leads to issues like:
- Key loss
- Unauthorized duplication of keys
- Absence of responsibility for the use of keys
- Delay in gaining access to restricted areas
If physical keys give access to critical infrastructure, poor key management poses risks to organizations. Modern-day technologies solve this problem by keeping physical keys safe and tracking all access attempts.
How Key Management System Enhancements for Security Improvement
A contemporary key management system improves the security status of enterprises through the digitalization of the process of key storage, usage, and monitoring. Instead of manual registers, such systems apply electronic lockers along with special software.
Among the most valuable enhancements made by key management systems are:
- Limited Access to Keys
Keys cannot be retrieved from the system by everyone; only authorized employees have the ability to gain access to specific keys via passwords, RFID tags, fingerprints, etc.
- Automatic Monitoring
Each operation connected with key retrieval is recorded, including information on the identity of the person involved, the date, and the time of the event. It helps create a detailed audit trail of all operations.
- Prevention of Key Loss
The system informs the administrator in case the key is not returned within the prescribed period, which greatly minimizes the risks of losses.
- Enhanced Productivity
Accessing the keys becomes faster because there is no need to spend extra time looking for them or contacting other staff members.
Key Features of Contemporary Key Management Systems
Contemporary enterprise software solutions provide sophisticated functionalities to ensure higher levels of safety and efficiency. The most important features of such systems are listed below.
- Safe Key Storage
The keys are kept in smart lockers with electronically locked compartments that unlock only after the successful authentication of the user.
- User authentication
The users must prove their identity by giving their biometric data, swiping their RFID badges, or even typing passwords.
- Automatic Key Logging
The solution tracks all key transactions performed and creates log files with information about each transaction.
- Reporting and Auditing Capabilities
The manager is able to create comprehensive reports that will help them analyze the key access history.
- Integration with Security Software Solutions
The contemporary systems can easily be connected with other security systems of the company and used for managing both keys and keyless access control systems.
Industries in India Reaping Benefits From Intelligent Key Management Systems
Intelligent key management systems. There are numerous industries within India that have implemented advanced key management systemsin order to improve their security infrastructure.
- IT Parks and Corporate Offices
Big campuses need to ensure restricted entry into conference halls, server rooms, and restricted floors
- Production Units
Production companies require stringent security measures in equipment rooms and maintenance rooms.
- Logistics and Warehouses
Warehouses need efficient management of secure access to storage spaces, vehicle keys, and loading docks.
- Healthcare Sector
Hospitals need better access management for medicine storage rooms, laboratories, and administration.
All these industries have realized significant benefits from implementing advanced key management systems.
Physical Security for Enterprises – The Future
With the rise in digitalization within the business world, security measures have been evolving, too. Today, key management solutions are often incorporated into advanced security technologies, including biometrics and Internet of Things-based monitoring and access control systems.
Such invitations enable companies to keep track of their keys through one platform, while ensuring maximum security. In light of increasing security regulations, automated key control is becoming a necessary measure for enterprises to ensure the safety of their property and premises.
Best Practices for Adopting Key Management Systems
There are a number of considerations when it comes to adopting a key management systemeffectively. The most important step is to formulate a security plan and to conduct the necessary staff training.
The critical entry points, like the server room, warehouse, and office doors, need to be defined. The role-based permissions must be assigned, as it allows only authorized people to access relevant keys.
Final Thoughts
While the management of physical keys could appear trivial, they contribute significantly to the protection of enterprise infrastructures. A properly executed key management systemprovides secure storage of keys, restricted access by authorized individuals only, and comprehensive tracking of key utilization. This ultimately leads to greater visibility, a reduction in the number of lost keys, and enhanced overall physical security.
For those enterprises looking to improve their security infrastructure, it might be worth considering the range of key management system options provided by DAccess. These help organizations build secure systems, improving efficiency along the way.